Receive suspicious calls or transaction records with your personal data exposed.
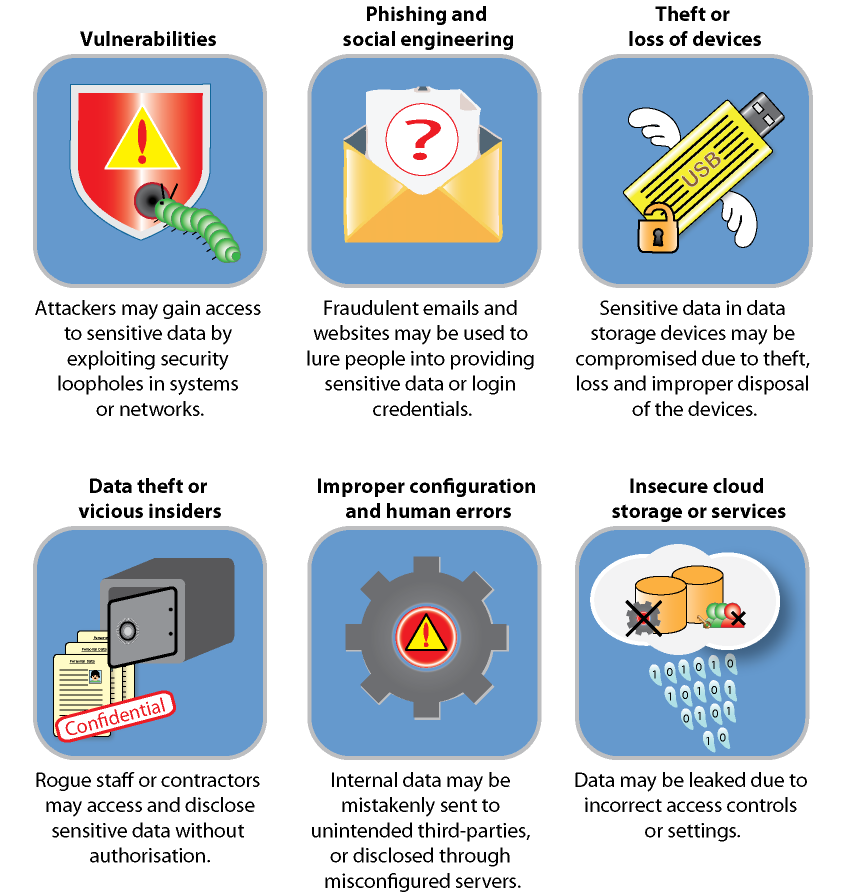
Data breach is a suspected breach of sensitive data by exposing the data to the risks of accidental loss, or unauthorised or accidental access, processing, erasure or use. Data breaches could result from cyber attacks to computer systems, networks or cloud storage during which cyber criminals gain unauthorised access to sensitive data such as personal data and financial data. Besides outsiders, data breaches could be caused by vicious insiders (e.g. privilege abuse), human errors (e.g. security misconfiguration) and negligence of users (e.g. loss of USB drive).
Typically, cyber criminals will target personal data such as name, identity card number, email address, username, password, credit card number or any data that can be used for criminal or dishonest purposes (e.g. deception). For businesses, valuable data such as financial record, intellectual property, trade secret and customer data can be targeted by cyber criminals for financial gain.
Signs indicating that you may have fallen victim to data breach:
Receive suspicious calls or transaction records with your personal data exposed.

Receive data breach notifications from government agencies (e.g. the Office of the Privacy Commissioner for Personal Data (PCPD)) or organisations holding your personal data.

Detect email accounts being compromised or involved in data breach incidents based on some reference sources such as "Have I Been Pwned".

Detect suspicious activities in your accounts.
You may consider taking the following measures:

Contact the respective service providers of your compromised accounts and check for any suspicious transactions.

Reset the password of any of your online accounts suspected to have been compromised.

Stay vigilant against phishing emails or other attempted scams using the breached data.

Consider reporting the case to the Hong Kong Computer Emergency Response Team Coordination Centre and the Police

Take appropriate actions to remove the breached data from public access (e.g. submit requests to the administrator of the websites and forums concerned).
Some references on data breach and what you need to know:
Disclaimer: Users are also recommended to observe the Important Notices of this website and read the user agreements and privacy policies of the security software and tools before download and use them.
