Beware of Malware Infection
Slide
1
/
of
Learning Purpose
Malware can cause different level of security risks to computer assets, such as disrupt computer operations, gather sensitive information, etc. This course introduces the threat and cause of malware infection. Security tips to protect your computing device from malware (including ransomware) infection will also be provided.

(Image source: PresenterMedia.com)
What is malware?
- Malware is a short name for malicious software. Cyber criminals spread malware that get installed on your computer or mobile device without your consent to steal sensitive information or disrupt the operation of your computing device.
- Common types of malware include computer virus, worms, Trojan Horse, spyware, adware, rootkit, botnets, logical bombs, backdoor, keylogger, scareware, and ransomware, etc.
- Some malware are able to exhibit multiple behaviours, e.g. certain program may be a virus and a Trojan Horse at the same time.
Risks of malware infection?
- Malware can cause damage or undesirable effects to computers or networks. Potential damage can include
- locking, modifying, destroying or stealing data
- gaining or allowing unauthorised access to a system
- executing functions that a user never intended
- disrupting or disabling the computer system and network
- demanding victim to pay ransom
- Malware poses a serious threat to data and information processing facilities. Users must take precautions to protect their computing devices from malware attack.

(Image source: https://blog.malwarebytes.org/101/2013/10/cryptolocker-ransomware-what-you-need-to-know/ and PresenterMedia.com)
Preventive measures
- Install anti-malware software to protect your machine and apply an up-to-date virus signature file regularly
- Install and enable a personal firewall
- Install the latest security patches for operating system and software
- Backup important data frequently and keep the backup data disconnected from the computer
- Turn on the security features such as phishing and malware protection on the web browser
- Schedule a daily scan to check for malware
(Image source: PresenterMedia.com)
Preventive measures (Continued)
- Do not open any suspicious emails, attachments and hyperlinks
- Do not visit suspicious websites or downloading any files from them
- Do not click or download anything from an unexpected pop-up windows or warnings from a program that you did not install or do not recognise
- Do not use software from a dubious source under any circumstances
- Disable the AutoRun feature on the CD/DVD Rom drive and USB storage devices
- Disable macros for Microsoft Word, Excel and other office applications by default
Possible symptoms being infected
The following symptoms may indicate a computer is infected with a malware:
- A program takes longer time than usual to execute
- A sudden reduction in available disk space
- A number of unknown or new files, programs or processes on the computer
- Popping up of new windows or browser advertisements
- Abnormal restarts or shutdowns of the computer
- An increase in network usage
- Change of system settings, such as change of default page of web browser
- Shutdown of security software (It cannot be restarted or updated.)
- Ransomware makes large number of files inaccessible and rename files with an unknown file extension (e.g. .locky, .encrypted, .crytolocker)
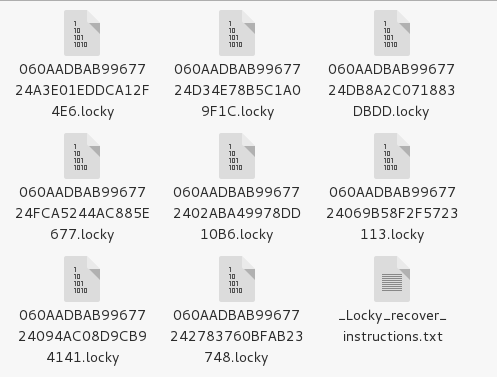
(Image source: https://blog.malwarebytes.org/threat-analysis/2016/03/look-into-locky/)
What can I do when infected?
In case a computer device is infected, users could consider to take the following immediate actions:
- Disconnect the infected computer device from the network to avoid further damage.
- If you suspect the computer is infected by ransomware, power off the computer to stop the ransomware encrypting more files.
- For other types of malware, scan and disinfect the computer with an anti-malware software.
- Jot down what have been accessed (such as programs, files, emails and websites) before discovering the issue.
- Do not open any file before clearing the malware.
- Restore data from the backup where appropriate.
- Report to the Police if criminal offence is involved.

(Image source: PresenterMedia.com)
Conclusion
- Do not open attachments or click any link in suspicious email, instant message or social network website.
- Do not visit suspicious websites or download any files from them.
- Install anti-malware software, personal firewall, and latest security patches for operating system and software.
- Backup your programs and data regularly. Keep the backup data disconnected from the computer









